If your team is actively evaluating Splunk alternatives, you are in good company. Splunk built its reputation as the dominant platform for log management, security monitoring, and operational intelligence, but rising licensing costs, proprietary query languages, and architectures that predate cloud-native infrastructure have pushed many teams to look elsewhere.
This guide is for engineering teams, platform engineers, DevOps practitioners, and security professionals searching for a Splunk replacement. Whether your priority is cutting costs by 60 to 80 percent, adopting open standards like OpenTelemetry, maintaining control over where your data lives, or simply finding a query interface your entire team can use without a certification program, there is a credible alternative available today.
We evaluated ten Splunk competitors across pricing model, deployment flexibility, OpenTelemetry support, query experience, and security fit. Each tool is described with real buyer trade-offs, not vendor marketing copy.
Why teams look for Splunk alternatives
Splunk remains a capable platform. The reasons teams seek Splunk alternatives are nonetheless consistent and structural.
Cost at scale. Splunk's pricing, historically anchored to daily ingest volume in gigabytes, is one of the most widely cited pain points in enterprise software. Teams that grow logging volume modestly can see annual spend climb into six figures without a meaningful increase in features or visibility.
Vendor lock-in. Splunk Search Processing Language (SPL) is powerful but entirely proprietary. Once your team has built hundreds of dashboards, alerts, and saved searches in SPL, migrating requires a significant rewrite effort regardless of which alternative you choose.
Cloud-native misalignment. Splunk was designed for a different era of infrastructure. Modern teams running on Kubernetes, instrumenting with OpenTelemetry, and storing data in object storage want a platform built around those primitives from the ground up, not one retrofitting cloud features onto a legacy index architecture.
Query language friction. SPL has a steep learning curve. Teams that need analysts, product managers, or on-call engineers without deep Splunk expertise to query logs regularly hit a wall. SQL-based and natural-language query interfaces lower that barrier significantly.
Open standards resistance. The observability ecosystem has converged on OpenTelemetry as the instrumentation standard. Splunk's OTLP support has improved over time, but teams building on open standards often prefer a platform designed around OTel natively rather than one that added support as an afterthought.
What to look for in a Splunk alternative
Not every Splunk alternative is suitable for every use case. These are the evaluation criteria that matter most.
Total cost of ownership. Ingest pricing tells only part of the story. Evaluate retention costs, query costs, user seat costs, and the engineering overhead of operating the platform. A self-hosted open source Splunk alternative may carry zero licensing cost but significant operational cost in engineering hours.
OpenTelemetry compatibility. If your team has adopted or plans to adopt OTel for instrumentation, your observability platform should accept OTLP natively without requiring an intermediate transformation layer. Platforms built after OTel matured handle this more cleanly than platforms that added support later.
Query language and analyst accessibility. SQL is understood by a far wider pool of engineers and analysts than SPL, LogQL, or NRQL. Natural language querying lowers the barrier further. Consider who will actually write queries in production and choose accordingly.
Deployment flexibility. Do you need to keep data in your own cloud account for compliance, data residency, or security reasons? Look for platforms offering self-hosted, BYOC (bring your own cloud), or on-premises deployment. SaaS-only platforms limit your data sovereignty options by design.
Unified observability vs. point solution. Some tools handle logs only. Others unify logs, metrics, and traces in a single platform. If your team is consolidating observability tooling, a unified platform reduces context switching and integration overhead.
SIEM and security relevance. If your use case includes security monitoring, threat detection, or audit logging, filter the list to tools with genuine SIEM capabilities or security-focused editions. Not every observability platform is a credible Splunk replacement for security operations.
10 Best Splunk Alternatives in 2026
At a glance: Splunk alternatives compared
| Tool | Best For | Pricing Model | OTel Support | Self-hosted / BYOC | Query Language | SIEM Fit | Main Trade-off |
|---|---|---|---|---|---|---|---|
| Parseable | Cloud-native unified observability | Per GB ingested | Native OTLP | Yes (OSS, BYOC, Cloud) | SQL + Natural Language | Audit logs, SIEM export | Newer ecosystem vs. Splunk |
| Elastic | Full-text search at scale | Compute + storage | Yes | Yes (self-hosted or Cloud) | DSL, EQL, KQL | Strong (Elastic Security) | High operational complexity |
| Datadog | APM-first cloud observability | Per host + per GB | Yes | No (SaaS only) | Datadog query language | Cloud SIEM (add-on) | Very expensive at scale |
| Grafana + Loki | Self-hosted open source stack | Per GB (Cloud) | Via OTel Collector | Yes (Loki OSS) | LogQL | Limited native SIEM | High engineering overhead |
| New Relic | Usage-based full-stack observability | Per GB + per user | Yes | No (SaaS only) | NRQL | Limited | Per-user costs add up |
| Dynatrace | AI-driven full-stack monitoring | Per host + per GB | Yes | Limited (primarily SaaS) | DQL | Some security features | Opaque pricing, high cost |
| Graylog | Lightweight centralized log management | Open source free / Enterprise | Via Beats/Syslog | Yes | Graylog / Lucene syntax | Graylog Security (add-on) | Requires separate search backend |
| SigNoz | OTel-native open source observability | Per GB + base fee | Native | Yes (OSS, BYOC) | ClickHouse SQL | Limited | Smaller ecosystem |
| Cribl | Log routing and pipeline control | Per GB/day (tiered) | Yes | Yes | N/A (routing layer) | Feeds SIEM tools | Not a storage or analytics backend |
| Sumo Logic | Cloud-native SIEM and log analytics | Credit-based / custom | Yes | No (SaaS only) | Sumo Logic Query Language | Strong (Cloud SIEM) | SaaS-only, proprietary query language |
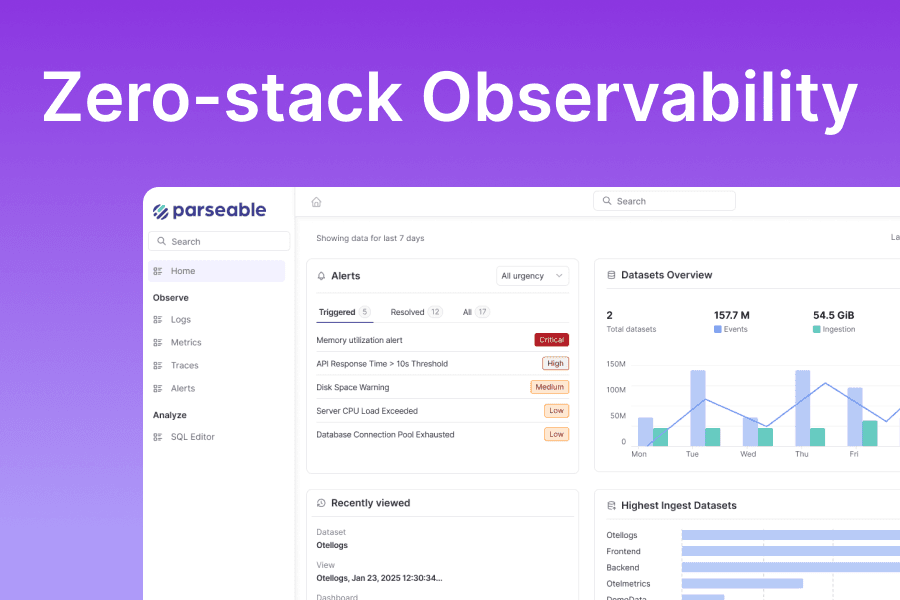
1. Parseable: Best Splunk Alternative for Cloud-Native Unified Observability
Parseable is an open source, cloud-native observability platform built in Rust that positions itself directly as a modern Splunk replacement. Where Splunk indexes data into a proprietary store, Parseable writes directly to Apache Parquet files on S3-compatible object storage. Your data lives in an open format you fully control, in your own bucket, at infrastructure-level storage costs.
The architecture delivers up to 90% data compression through columnar storage design, which translates directly into lower storage costs compared to index-based platforms like Splunk. Ingestion is OpenTelemetry-native: OTLP over HTTP and gRPC is supported out of the box alongside the full ecosystem of agents including Fluent Bit, Fluentd, Vector, Filebeat, and Logstash. You can also ingest from Kafka, Redpanda, AWS Kinesis, Azure Event Hubs, and GCP Pub/Sub without a transformation middleware layer. See the full list of supported sources on the Parseable integrations page.
Rather than forcing teams to learn SPL or a proprietary query language, Parseable offers SQL-based analysis and natural language querying. The platform's AI-first design means your engineers, analysts, and on-call teams can query telemetry data in plain English or write SQL without needing a dedicated training program.
Parseable unifies logs, metrics, and traces in a single interface. AI-native capabilities include predictive forecasting, anomaly detection, real-time alerting, unlimited dashboards, and granular access control with OAuth2 and federated IAM support. The security integration story is verified: Parseable supports Falco, Trivy, and SIEM export from its integrations catalog, with 50+ total integrations across visualization tools, cloud providers, streaming platforms, CI/CD systems, and LLM/AI agent frameworks.
Deployment is genuinely flexible. The open source version (Parseable OSS) runs entirely self-hosted in standalone or distributed mode on Docker, Kubernetes, or any major cloud. Parseable Cloud is the managed offering. BYOC (bring your own cloud) runs Parseable infrastructure inside your own AWS, GCP, or Azure account. The Enterprise plan adds Apache Iceberg support, dedicated infrastructure, and custom data residency. Explore all deployment options in the Parseable docs.
Pricing (verified from parseable.com/pricing):
- OSS: Free, self-hosted, no licensing
- Pro: $0.39/GB ingested, 365-day retention, shared infrastructure, 14-day free trial
- Enterprise: Starts at $15,000/year, dedicated infrastructure, BYOC, self-hosted, custom retention with Iceberg support
- Additional query scanning beyond 10x monthly ingest: $0.02/GB
Pros:
- Data stored in open Apache Parquet format on your own S3 bucket with no proprietary lock-in
- OpenTelemetry-native OTLP ingestion requires no transformation layer
- SQL and natural language querying accessible to non-specialists
- Unifies logs, metrics, and traces in one platform
- Up to 90% storage compression reduces cost significantly versus index-based platforms
- Three deployment modes: OSS (free), managed cloud, BYOC, and on-premises
- 50+ integrations covering Kafka, Kubernetes, Grafana, all major cloud providers, and AI/LLM frameworks
- AI-native forecasting, anomaly detection, and alerting built in
- Built in Rust for performance and low operational footprint
Cons:
- Younger platform with a smaller community than Elastic or Splunk
- Enterprise features including dedicated infrastructure and Iceberg support require the $15,000/year plan
- Natural language querying, while genuinely useful, is a newer capability than battle-tested SPL equivalents
Ready to see what Parseable looks like on your own data? Try Parseable free with the OSS version or start a 14-day Pro trial at $0.39/GB.
2. Elastic: Splunk Alternative for Full-Text Search at Scale
Elastic, and the broader ELK Stack (Elasticsearch, Logstash, Kibana), has been the dominant open source Splunk alternative for nearly a decade. The core value proposition is powerful full-text search across large log volumes, paired with a mature ecosystem of ingestion tools, dashboards, and machine learning capabilities.
Elasticsearch as a search engine is best-in-class for unstructured text search. If your use case centers on searching log messages at high volume with low latency, Elastic delivers. Elastic Security extends the platform into genuine SIEM territory with threat detection, user and entity behavior analytics (UEBA), and endpoint protection, making it a credible Splunk replacement for security operations teams with existing ELK expertise.
The trade-off is operational complexity. Running Elasticsearch well at scale requires JVM heap tuning, shard allocation strategy, index lifecycle policy management, and ongoing cluster health monitoring. Self-hosted deployments at high ingest volumes become a significant platform engineering commitment. Elastic Cloud (managed) reduces that overhead but changes the cost structure considerably.
Note: Elastic's licensing changed in 2021 to the Elastic License 2.0 and SSPL, which restricts certain commercial use cases. OpenSearch (the AWS-maintained fork) remains fully open source under Apache 2.0 if license terms are a concern.
Pricing: Elastic offers a free open source tier for self-hosted deployments. Elastic Cloud provides serverless and hosted managed options, both accessible via free trial. Hosted Cloud pricing scales with compute and storage consumed; consult elastic.co/pricing directly for current rates, as serverless and hosted configurations carry different pricing structures.
Pros:
- Industry-leading full-text search capabilities across large log volumes
- Large, mature open source community with extensive documentation and tooling
- Strong SIEM product (Elastic Security) with built-in threat detection and UEBA
- Multiple deployment options: self-hosted OSS, Elastic Cloud serverless, and hosted
- Broad OTel compatibility
- Kibana provides rich visualization and dashboarding capabilities
Cons:
- Self-hosted Elasticsearch is operationally demanding: JVM tuning, shard management, and index lifecycle policies require dedicated expertise
- Licensing changed in 2021 (SSPL / Elastic License 2.0), creating ambiguity around open source status
- Elastic Cloud costs scale steeply with data volume
- Query DSL and EQL have a high learning curve for less technical users
- Cluster management adds significant platform engineering overhead at scale
3. Datadog: Splunk Alternative for Cloud-Native APM and Log Management
Datadog is the dominant SaaS observability platform for cloud-native engineering teams. It unifies infrastructure monitoring, APM, log management, real user monitoring, synthetic testing, and Cloud SIEM in a single product suite, which makes it appealing for teams that want broad coverage without integrating multiple tools.
As a Splunk alternative for log management, Datadog's primary strength is seamless correlation between logs, traces, and metrics. When debugging a production incident, being able to pivot from a slow trace directly to correlated logs without switching products is genuinely valuable. The platform also offers out-of-the-box parsing for 200+ log sources and a log management UI that most teams find accessible.
The honest limitation is cost. Datadog's pricing is multi-dimensional: host agents, ingested GB, indexed log events, retained metrics, and individual product modules are all billed separately. Teams frequently find that enabling the full feature set they need pushes annual spend into the $50,000 to $150,000+ range for mid-sized infrastructure. There is no self-hosted option, which limits data sovereignty choices to Datadog's available regions.
Pricing (verified from datadoghq.com/pricing):
- Log ingestion: $0.10/GB/month
- Standard indexing at 15-day retention: $1.70/million log events/month
- Flex Storage: $0.05/million events/month (up to 15 months retention)
- No free tier for logs; trials available
Pros:
- Best-in-class APM and infrastructure monitoring with seamless log correlation
- Out-of-the-box parsing for 200+ log sources reduces setup time
- Single UI to pivot between logs, traces, and metrics
- Strong alerting, anomaly detection, and dashboarding
- Cloud SIEM available as an add-on product
Cons:
- SaaS only; no self-hosted or BYOC deployment option limits data sovereignty
- Multi-dimensional pricing (per host, per GB, per indexed event, per module) makes cost estimation unreliable
- Full feature enablement routinely costs $50,000 to $150,000+/year for mid-sized teams
- Proprietary Datadog query language creates migration lock-in
- Agent-based model adds per-host cost overhead that compounds at scale
4. Grafana + Loki: Open Source Splunk Alternative for Self-Hosted Teams
The Grafana and Loki combination is the most widely used open source Splunk alternative for teams comfortable with infrastructure operations. Loki is Prometheus-inspired log aggregation designed by Grafana Labs: it indexes only metadata labels rather than full log content, keeping storage costs low at the cost of making full-text search across unindexed fields slower at query time.
Grafana itself is the de facto open source visualization standard in observability. Paired with Loki for logs, Tempo for traces, and Mimir or Prometheus for metrics, teams can build a fully unified observability stack without per-GB SaaS pricing. The Grafana Cloud managed offering makes this accessible without the self-hosting operational burden.
The real trade-off is engineering investment. A self-hosted Loki deployment at high ingest scale requires tuning chunk cache size, managing compaction jobs, planning storage backends, and operating multiple interconnected components. Teams that want the cost savings of a self-hosted Splunk alternative should factor in the ongoing platform engineering hours.
Pricing (verified from grafana.com/pricing):
- Free tier: 50GB logs/month, 14-day retention, no credit card required
- Pro: $19/month platform fee plus $0.50/GB logs ingested, 30-day retention
- Enterprise: $25,000/year minimum, custom pricing and retention
Pros:
- Loki is free open source software; self-hosted deployments carry no licensing cost
- Grafana is the most widely adopted open source dashboard tool in observability
- Grafana Cloud offers a generous free tier and straightforward per-GB log pricing
- Strong OTel support via the OpenTelemetry Collector
- Active community, large plugin ecosystem, and broad vendor support
Cons:
- Loki's label-based indexing limits full-text search performance; queries on unindexed fields are slow
- Self-hosting the full stack (Grafana, Loki, Tempo, Mimir, OTel Collector) is operationally complex
- LogQL requires dedicated learning and is less widely known than SQL
- No native SIEM capabilities; security use cases require significant additional tooling
- Grafana Cloud costs scale with usage; the free tier is limited for most production workloads
Comparing Grafana + Loki with a simpler alternative? See how Parseable handles unified observability when you want SQL-native querying, OTLP-first ingestion, and a single platform instead of a multi-component stack.
5. New Relic: Splunk Alternative for Usage-Based Full-Stack Observability
New Relic transitioned from per-host pricing to a consumption-based model centered on data ingest and user seats. The result is a full-stack observability platform that is often more cost-predictable at moderate scale than Splunk or Datadog, particularly for smaller teams that stay within the generous free tier.
The 100GB/month free ingest tier is a genuine differentiator when evaluating Splunk replacements. For teams logging a few hundred thousand events per day, New Relic can function as a zero-cost observability platform. Beyond the free tier, the per-GB ingest pricing applies uniformly across logs, metrics, and traces, which simplifies estimation compared to tools with separate per-signal pricing.
New Relic's limitations as a pure Splunk alternative for log management center on query language and security fit. NRQL (New Relic Query Language) is more accessible than SPL but remains proprietary and requires dedicated learning. The platform lacks strong native SIEM capabilities, making it a poor fit for security operations teams seeking a Splunk replacement.
Pricing (verified from newrelic.com/pricing):
- Free tier: 100GB/month ingest, 1 full platform user, unlimited basic users
- Beyond free: $0.40/GB ingested (Original data) or $0.60/GB (Data Plus, with extended retention and advanced governance)
- Standard: $10/first full user, $99/additional full user
- Pro: $349/user/year (annual) or approximately $419/user/month (monthly)
- Enterprise: Custom pricing
Pros:
- 100GB/month free ingest is genuinely useful for small teams and evaluation
- Unified platform covers APM, infrastructure, browser, mobile, and logs in one product
- No per-host pricing; consumption model scales more predictably than agent-based platforms
- Good OTel support with guided onboarding
- Accessible UI for teams new to observability
Cons:
- SaaS only; no self-hosted or BYOC deployment option
- NRQL is proprietary and adds a learning curve for teams coming from SQL environments
- Per-user charges (Pro at $349/user/year) inflate costs significantly for larger engineering teams
- Limited SIEM capabilities; not a credible Splunk replacement for security operations
- $0.40/GB ingest pricing beyond the free tier is relatively high for log-heavy workloads
6. Dynatrace: Splunk Alternative for AI-Driven Full-Stack Monitoring
Dynatrace is a premium observability and AIOps platform that differentiates itself through the Davis AI engine, automatic dependency mapping via Smartscape, and deterministic root cause analysis. It is one of the few platforms that can credibly claim to reduce alert noise through causal AI rather than simple threshold-based alerting.
For teams evaluating Dynatrace as a Splunk alternative, context is important. Dynatrace delivers the most value for large enterprise environments where the priority is reducing mean time to resolution (MTTR) across complex distributed systems, particularly those with legacy Java and JVM workloads where full-stack auto-instrumentation generates clear value. It is less suitable for teams primarily focused on log analytics, cost efficiency, or self-hosted deployment.
The pricing model is among the most complex in the observability market. Log analytics is billed separately from APM, and the choice between pay-per-query and bundled query models requires careful planning to avoid bill surprises.
Pricing (verified from dynatrace.com/pricing):
- Log ingestion: $0.20/GiB
- Log retention: $0.0007/GiB-day (pay-per-query) or $0.02/GiB-day (bundled, 10-35 days included)
- Full-Stack Monitoring: $58/month per 8GB host
- Infrastructure Monitoring: $29/month per host
Pros:
- Davis AI provides genuine automated root cause analysis, not just anomaly flags
- Smartscape topology mapping is powerful for complex distributed architectures
- Grail data lakehouse provides unified storage for logs, metrics, and traces
- Strong support for enterprise Java/JVM environments with deep auto-instrumentation
- Comprehensive security posture management and runtime protection add-ons
Cons:
- Pricing complexity makes cost estimation difficult; billing surprises are common
- Primarily SaaS with limited self-hosted deployment options
- DQL (Dynatrace Query Language) requires dedicated learning time
- Per-host pricing model adds cost pressure in dynamic Kubernetes environments
- Overkill and over-priced for teams primarily focused on log management and search
7. Graylog: Splunk Alternative for Lightweight Centralized Log Management
Graylog is an open source log management platform with a long track record in enterprise deployments. It is one of the most straightforward self-hosted Splunk alternatives for teams that need centralized log collection, search, and alerting without the full operational complexity of a managed ELK stack.
Graylog uses Elasticsearch or OpenSearch as its underlying search backend and MongoDB for metadata and configuration storage. The Graylog interface is widely regarded as more accessible than raw Kibana, and its search syntax (based on Lucene query syntax) is approachable for teams familiar with basic search queries. Graylog Security extends the platform into SIEM territory with threat detection, anomaly-based alerting, and compliance reporting, making it a more versatile Splunk alternative for security-adjacent use cases.
As an open source Splunk alternative, Graylog's strongest advantage is simplicity relative to a full ELK deployment. Smaller teams that want a working log management platform without tuning Elasticsearch shards or building Kibana from scratch often find Graylog a practical starting point.
Pricing: The open source version (Graylog Operations) is free for self-hosted use. Enterprise and Cloud tiers with security features and managed hosting are available; pricing for those tiers requires contacting Graylog's sales team.
Pros:
- Fully open source core with no licensing cost for self-hosted deployments
- More accessible UI than raw Kibana for teams without dedicated Elastic expertise
- Graylog Security extends the platform into SIEM use cases with threat detection and compliance
- Lucene-based search syntax is intuitive and familiar
- Enterprise support available for production deployments
Cons:
- Requires operating Elasticsearch or OpenSearch as a separate backend, adding complexity
- MongoDB dependency introduces another operational component to manage
- Performance at high ingest volumes requires substantial infrastructure investment
- Enterprise and Security edition pricing requires contacting sales with no self-serve transparency
- Designed primarily for on-premises or VM deployments; not cloud-native by architecture
8. SigNoz: Open Source Splunk Alternative Built on OpenTelemetry
SigNoz is an open source observability platform built natively on OpenTelemetry and ClickHouse. It provides unified logs, metrics, and traces with a UI designed around OTel concepts, making it the most natural self-hosted Splunk alternative for teams that have fully committed to OpenTelemetry instrumentation and want a backend they can run themselves.
The ClickHouse-based storage layer gives SigNoz strong analytical query performance on log data at scale. Users run SQL-compatible queries directly on their telemetry, which is a meaningful usability advantage over platforms requiring proprietary query languages. The cloud offering adds managed hosting with SOC2 Type II and HIPAA compliance, and deployment flexibility extends to dedicated cloud, BYOC, or self-hosted with a support contract at the Enterprise tier.
As a Splunk alternative, SigNoz is most compelling for engineering teams on tighter budgets who want the observability capabilities of a full-stack platform without a vendor pricing model. The community edition is production-capable, and the gap between OSS features and paid features is narrower than most commercial alternatives.
Pricing (verified from signoz.io/pricing):
- Community: Free, self-hosted open source
- Teams (Cloud): Starting at $49/month (includes $49 usage credit); logs at $0.30/GB ingested, traces $0.30/GB, metrics $0.10/million samples
- Enterprise: Custom pricing from $4,000/month; dedicated cloud, BYOC, or self-hosted with support
Pros:
- Fully OpenTelemetry-native; no proprietary instrumentation or agents required
- Open source community edition is free and production-capable
- ClickHouse-backed storage enables fast analytical queries at scale
- SQL-compatible querying lowers the barrier versus SPL or proprietary DSLs
- Flexible deployment: cloud, BYOC, or fully self-hosted
- SOC2 Type II and HIPAA compliant on the cloud offering
- Competitive pricing compared to Datadog and New Relic
Cons:
- Smaller ecosystem and community than Elastic, Grafana, or legacy platforms
- Limited SIEM capabilities; not a credible Splunk replacement for security operations
- Teams Cloud pricing at $0.30/GB for logs is higher than some open source alternatives
- Enterprise plan starts at $4,000/month, a steep jump from the Teams tier
- Fewer pre-built integrations and dashboards than more established platforms
Evaluating open source Splunk alternatives? Compare Parseable against your current stack and see what $0.39/GB gets you with native OTLP ingestion, SQL querying, and data stored in your own S3 bucket in open Apache Parquet format.
9. Cribl: Splunk Alternative for Log Routing, Enrichment, and Pipeline Control
Cribl Stream occupies a fundamentally different position from every other tool on this list. It is not a log storage or analytics platform. It is a vendor-agnostic data pipeline for observability telemetry: it receives logs, metrics, and traces from any source and routes, filters, transforms, redacts, and enriches that data before forwarding it to any destination, whether that is your existing SIEM, Splunk itself, or any Splunk alternative.
For teams not ready to fully migrate away from Splunk, Cribl is commonly used to filter out low-value log data before it reaches Splunk's ingest tier, directly reducing the license-driving data volume. For teams actively replacing Splunk, Cribl provides the ingestion and routing layer that enables parallel delivery to a new backend during a transition period. Cribl Edge adds agent-level collection, and Cribl Search enables federated query across multiple storage backends without requiring full data centralization.
Pricing: Cribl Stream offers a free tier for up to 1TB/day of data processing. Beyond that, pricing scales with volume and is available by contacting Cribl's sales team. Both cloud-managed and self-managed deployment options are available.
Pros:
- Vendor-neutral pipeline reduces Splunk ingest costs without requiring a full migration
- Supports all major observability sources and destinations
- Valuable for data redaction, PII masking, and compliance before log ingestion
- Useful bridge during a migration from Splunk to any alternative backend
- Cribl Search enables federated query across existing storage without moving data
Cons:
- Not a log storage or analytics backend; requires a separate destination platform
- Adds another operational component to manage in your observability stack
- Primary value is cost reduction and routing, not direct observability capability
- Pricing beyond the 1TB/day free tier requires engaging sales with no published rates
- Teams primarily focused on log analytics and search need a different tool in addition to Cribl
10. Sumo Logic: Cloud-Native Splunk Alternative for SIEM and Log Analytics
Sumo Logic is a cloud-native platform that has competed directly with Splunk in enterprise log management and security analytics for over a decade. It delivers a unified product covering log analytics, infrastructure monitoring, Cloud SIEM, and threat intelligence in a SaaS model that removes the operational burden of managing observability infrastructure.
As a Splunk alternative for security operations, Sumo Logic is one of the more credible options in the market. Its Cloud SIEM product includes built-in threat detection rules, entity behavior analytics, and compliance reporting. For compliance-heavy organizations looking to move off Splunk without sacrificing SIEM depth, Sumo Logic warrants serious evaluation.
The platform uses a credit-based pricing model that bundles ingest, storage, and queries into a unified consumption pool, which some organizations find more predictable than Splunk's GB/day licensing. The main limitations are the SaaS-only delivery model with no self-hosted path and the Sumo Logic Query Language, a proprietary syntax that creates its own migration overhead if you later switch platforms.
Pricing: Sumo Logic uses a credit-based consumption model; specific per-unit pricing and plan details require contacting their sales team. A free trial is available. Enterprise and Cloud Flex plans are offered.
Pros:
- Strong Cloud SIEM product with built-in threat detection and entity behavior analytics
- Cloud-native SaaS delivery; no infrastructure to manage or scale
- Credit-based model can be more predictable than per-seat or per-host pricing
- Long track record as a direct Splunk competitor in enterprise log management
- OTel ingestion supported; native integrations with AWS, Azure, and GCP
Cons:
- SaaS only; no self-hosted or BYOC deployment option limits data residency control
- Sumo Logic Query Language is proprietary, creating migration overhead if you switch later
- Pricing requires engaging sales; no self-serve pricing transparency
- Can be expensive at high ingest volumes relative to open source alternatives
- Some customers report the UI as less intuitive compared to newer entrants
How to choose the right Splunk alternative
The right Splunk replacement depends directly on the primary reason you are leaving Splunk.
If cost is the primary driver, start with Parseable OSS, SigNoz Community, or Grafana + Loki self-hosted. These three offer the lowest total licensing cost. Parseable OSS and SigNoz Community are free to run; both use open formats and open standards, limiting future migration friction. Factor in operational overhead when comparing self-hosted options against managed cloud pricing.
If compliance or data residency requires self-hosted or BYOC deployment, Parseable, Elastic, Graylog, and SigNoz all support on-premises or BYOC deployments. Parseable's BYOC model is architecturally clean because your data lives natively in your own S3 bucket in Apache Parquet format from day one, with no proprietary indexing layer between you and your data.
If OpenTelemetry is your instrumentation standard, Parseable and SigNoz are both designed around OTel from the ground up and accept OTLP natively. Elastic, Datadog, New Relic, and Grafana all support OTel but were built before the standard matured and treat it as one of several ingestion paths rather than the primary one. See Parseable's ingestion docs for a full breakdown of supported protocols and agents.
If SIEM capabilities are required, Elastic Security, Graylog Security, Sumo Logic Cloud SIEM, and Datadog Cloud SIEM are the options with genuine security operations depth. Parseable supports SIEM export and security-relevant integrations (Falco, Trivy) but positions primarily as an observability and log management platform.
If analyst accessibility is a priority, Parseable (SQL plus natural language), SigNoz (ClickHouse SQL), and Datadog (log query builder) all lower the barrier for less technical users compared to SPL. The ability to query in plain SQL has a disproportionate impact on team-wide adoption.
If you are not ready for full migration, Cribl Stream is a pragmatic first step that reduces Splunk ingest costs while you evaluate long-term alternatives. It is not a replacement, but it buys time and cuts cost without requiring architectural changes.
FAQ
What is the best Splunk alternative? For most cloud-native engineering teams, Parseable offers the strongest combination of cost efficiency, open standards alignment, and deployment flexibility. It stores data in Apache Parquet on your own S3 bucket, accepts OTLP natively, and supports SQL and natural language querying without proprietary lock-in. Try Parseable free.
What is the best open source Splunk alternative? Parseable OSS, Elastic (self-hosted), Graylog (open source core), SigNoz (community edition), and Grafana + Loki are all credible open source Splunk alternatives. Parseable and SigNoz are the most modern architecturally; Elastic has the largest community and deepest search capabilities; Graylog is the most accessible starting point for smaller teams.
Which Splunk alternative is best for SIEM? Elastic Security and Sumo Logic Cloud SIEM are the most fully featured SIEM alternatives to Splunk. Graylog Security is a credible option for organizations already on Graylog. Datadog Cloud SIEM works well for teams already using Datadog for infrastructure and APM monitoring.
Which Splunk alternative is best for log management? For pure log management, Parseable, Elastic, and Graylog are the strongest options. Parseable is best for teams prioritizing cost, open standards, and SQL-native querying. Elastic is best for teams prioritizing full-text search depth at scale. Graylog is best for teams wanting a lighter operational lift compared to a full ELK deployment.
Is there a self-hosted Splunk alternative? Yes. Parseable OSS, Elastic (self-hosted), Graylog, SigNoz Community, and the Grafana + Loki stack all support fully self-hosted deployment. Parseable OSS is free, stores data in open Apache Parquet format on any S3-compatible backend, and requires no licensing discussion.
What is the cheapest Splunk alternative? On a pure licensing basis, Parseable OSS, SigNoz Community, Graylog Open, and Grafana + Loki self-hosted are all free. For managed cloud options, the cost comparison depends on ingest volume. Parseable Pro at $0.39/GB and SigNoz Teams at $0.30/GB are among the most transparent per-GB cloud pricing options available. Both include a free trial or free-tier path.
Does Parseable support OpenTelemetry? Yes. Parseable supports OTLP over HTTP and gRPC natively, making it a clean destination for any OpenTelemetry Collector pipeline. It also supports traditional agents including Fluent Bit, Fluentd, Vector, Filebeat, and Logstash, as well as streaming platforms like Kafka and cloud-native sources like AWS Kinesis and Azure Event Hubs. See the full details on the Parseable ingestion docs.
Conclusion
The Splunk alternatives market in 2026 is more mature and capable than it has ever been. Teams have real choices across the full spectrum of requirements: from fully managed SaaS to completely self-hosted open source, from pure log management to unified observability with AI-native analysis, and from proprietary high-cost platforms to open standards-aligned alternatives that keep your data portable and your options open.
The most important shift is that modern Splunk alternatives no longer require you to trade capability for cost. Platforms like Parseable demonstrate that you can have OpenTelemetry-native ingestion, SQL and natural language querying, AI-driven anomaly detection, and unified logs, metrics, and traces across a single platform, all while storing data in open formats in your own infrastructure at a fraction of Splunk's ingest pricing.
If cost, vendor lock-in, or cloud-native alignment brought you to evaluate Splunk alternatives, Parseable is the logical starting point. The open source version is free with no license required, the Pro plan starts at $0.39/GB with a 14-day trial, and your data lives in Apache Parquet on your own S3 bucket from the first log line ingested.
Get started with Parseable and see how your observability stack changes when storage costs 80x less and queries run in plain SQL or plain English.
SEO Meta Title
10 Best Splunk Alternatives in 2026: Costs & Trade-offs
(55 characters)
SEO Meta Description
Compare 10 Splunk alternatives on cost, OTel support, deployment options, and query language. Find the best Splunk replacement for your team in 2026.
(149 characters)
Suggested URL Slug
/blog/splunk-alternatives
JSON-LD: BlogPosting / Article Schema
{
"@context": "https://schema.org",
"@type": "BlogPosting",
"headline": "10 Best Splunk Alternatives in 2026",
"description": "A comprehensive comparison of 10 Splunk alternatives covering cost, deployment options, OpenTelemetry support, query languages, and SIEM capabilities to help engineering and security teams find the right Splunk replacement.",
"author": {
"@type": "Organization",
"name": "Parseable",
"url": "https://www.parseable.com"
},
"publisher": {
"@type": "Organization",
"name": "Parseable",
"url": "https://www.parseable.com"
},
"dateModified": "2026-04-10",
"mainEntityOfPage": {
"@type": "WebPage",
"@id": "https://www.parseable.com/blog/splunk-alternatives"
},
"keywords": [
"Splunk alternatives",
"best Splunk alternatives",
"Splunk competitors",
"Splunk replacement",
"open source Splunk alternative",
"Splunk alternative for log management",
"Splunk alternative for SIEM",
"cloud-native Splunk alternative",
"self-hosted Splunk alternative",
"log management",
"observability",
"OpenTelemetry",
"SIEM"
],
"articleSection": "Observability and Log Management",
"about": [
{
"@type": "SoftwareApplication",
"name": "Parseable",
"url": "https://www.parseable.com"
}
]
}JSON-LD: ItemList Schema
{
"@context": "https://schema.org",
"@type": "ItemList",
"name": "10 Best Splunk Alternatives in 2026",
"description": "A ranked list of the best Splunk alternatives for log management, observability, and SIEM evaluated on cost, deployment flexibility, OpenTelemetry support, and query language.",
"url": "https://www.parseable.com/blog/splunk-alternatives",
"numberOfItems": 10,
"itemListElement": [
{
"@type": "ListItem",
"position": 1,
"name": "Parseable",
"description": "Cloud-native unified observability platform with OpenTelemetry-native ingestion, SQL and natural language querying, and data stored in Apache Parquet on your own S3 bucket.",
"url": "https://www.parseable.com"
},
{
"@type": "ListItem",
"position": 2,
"name": "Elastic",
"description": "Open source full-text search and observability platform with strong SIEM capabilities via Elastic Security. Available self-hosted or as a managed cloud service.",
"url": "https://www.elastic.co"
},
{
"@type": "ListItem",
"position": 3,
"name": "Datadog",
"description": "SaaS observability platform unifying APM, infrastructure monitoring, log management, and Cloud SIEM with seamless signal correlation.",
"url": "https://www.datadoghq.com"
},
{
"@type": "ListItem",
"position": 4,
"name": "Grafana and Loki",
"description": "Open source observability stack with Loki for log aggregation and Grafana for visualization. Available self-hosted or as a managed cloud offering.",
"url": "https://grafana.com"
},
{
"@type": "ListItem",
"position": 5,
"name": "New Relic",
"description": "Usage-based full-stack observability platform with a 100GB/month free ingest tier and unified coverage of APM, infrastructure, and logs.",
"url": "https://newrelic.com"
},
{
"@type": "ListItem",
"position": 6,
"name": "Dynatrace",
"description": "AI-driven full-stack monitoring platform with automatic root cause analysis, topology mapping, and a unified data lakehouse for logs, metrics, and traces.",
"url": "https://www.dynatrace.com"
},
{
"@type": "ListItem",
"position": 7,
"name": "Graylog",
"description": "Open source centralized log management platform with an accessible UI and a security edition for SIEM-adjacent use cases.",
"url": "https://www.graylog.org"
},
{
"@type": "ListItem",
"position": 8,
"name": "SigNoz",
"description": "OpenTelemetry-native open source observability platform with ClickHouse-backed log analytics and flexible deployment including self-hosted and BYOC options.",
"url": "https://signoz.io"
},
{
"@type": "ListItem",
"position": 9,
"name": "Cribl",
"description": "Vendor-agnostic observability data pipeline for routing, filtering, enriching, and transforming logs, metrics, and traces before delivery to any storage backend.",
"url": "https://cribl.io"
},
{
"@type": "ListItem",
"position": 10,
"name": "Sumo Logic",
"description": "Cloud-native log analytics and Cloud SIEM platform with built-in threat detection, entity behavior analytics, and compliance reporting.",
"url": "https://www.sumologic.com"
}
]
}JSON-LD: FAQPage Schema
{
"@context": "https://schema.org",
"@type": "FAQPage",
"mainEntity": [
{
"@type": "Question",
"name": "What is the best Splunk alternative?",
"acceptedAnswer": {
"@type": "Answer",
"text": "For most cloud-native engineering teams, Parseable offers the strongest combination of cost efficiency, open standards alignment, and deployment flexibility. It stores data in Apache Parquet on your own S3 bucket, accepts OTLP natively, and supports SQL and natural language querying without proprietary lock-in."
}
},
{
"@type": "Question",
"name": "What is the best open source Splunk alternative?",
"acceptedAnswer": {
"@type": "Answer",
"text": "Parseable OSS, Elastic (self-hosted), Graylog (open source core), SigNoz (community edition), and Grafana plus Loki are all credible open source Splunk alternatives. Parseable and SigNoz are the most modern architecturally. Elastic has the largest community and deepest search capabilities. Graylog is the most accessible starting point for smaller teams."
}
},
{
"@type": "Question",
"name": "Which Splunk alternative is best for SIEM?",
"acceptedAnswer": {
"@type": "Answer",
"text": "Elastic Security and Sumo Logic Cloud SIEM are the most fully featured SIEM alternatives to Splunk. Graylog Security is a credible option for organizations already on Graylog. Datadog Cloud SIEM works well for teams already using Datadog for infrastructure and APM monitoring."
}
},
{
"@type": "Question",
"name": "Which Splunk alternative is best for log management?",
"acceptedAnswer": {
"@type": "Answer",
"text": "For pure log management, Parseable, Elastic, and Graylog are the strongest options. Parseable is best for teams prioritizing cost, open standards, and SQL-native querying. Elastic is best for teams prioritizing full-text search depth at scale. Graylog is best for teams wanting a lighter operational lift compared to a full ELK deployment."
}
},
{
"@type": "Question",
"name": "Is there a self-hosted Splunk alternative?",
"acceptedAnswer": {
"@type": "Answer",
"text": "Yes. Parseable OSS, Elastic (self-hosted), Graylog, SigNoz Community, and the Grafana plus Loki stack all support fully self-hosted deployment. Parseable OSS is free, stores data in open Apache Parquet format on any S3-compatible backend, and requires no licensing discussion."
}
},
{
"@type": "Question",
"name": "What is the cheapest Splunk alternative?",
"acceptedAnswer": {
"@type": "Answer",
"text": "On a pure licensing basis, Parseable OSS, SigNoz Community, Graylog Open, and Grafana plus Loki self-hosted are all free. For managed cloud options, Parseable Pro at $0.39 per GB and SigNoz Teams at $0.30 per GB are among the most transparent per-GB cloud pricing options. Both include a free trial or free-tier path."
}
},
{
"@type": "Question",
"name": "Does Parseable support OpenTelemetry?",
"acceptedAnswer": {
"@type": "Answer",
"text": "Yes. Parseable supports OTLP over HTTP and gRPC natively, making it a clean destination for any OpenTelemetry Collector pipeline. It also supports traditional agents including Fluent Bit, Fluentd, Vector, Filebeat, and Logstash, as well as streaming platforms like Kafka and cloud-native sources like AWS Kinesis and Azure Event Hubs."
}
}
]
}